Cryptography
Apr 2, 2026
Gröbner Bases in Cryptanalysis Part2: Attacking Poseidon
Learn how Gröbner bases break cryptographic hash functions. We attack a reduced-round Poseidon instance, recovering a preimage from its dige...
Cryptography
Nov 12, 2025
Fix a field with . An algebraic closure of is denoted and is a field extension of where every non-constant polynomial with coefficients in has a root in .
An elliptic curve can be represented by a short Weierstrass equation
Such a curve is smooth (nonsingular) if and only if the discriminant
is nonzero, which simplifies to the condition . The -invariant of the curve, which will play a central role in the protocol, is defined as
Assume . We call supersingular if the only point satisfying is , equivalently, there are no nonzero -torsion points over . Otherwise the curve is ordinary.
Why supersingular curves.
A practical advantage of supersingular curves is that all supersingular -invariants lie in . Consequently, we can perform arithmetic entirely over the quadratic field , avoiding computations in higher extensions which are more expensive.
For , the -torsion subgroup consists of all points annihilated by multiplication by :
Let be a field with and an elliptic curve. Denote by the -torsion subgroup. Then
Equivalently,
while for ordinary curves one has .
Let's find the 2-torsion subgroup for the curve defined over . The definition of a 2-torsion subgroup is
If we visualize this, the 2-torsion points are the intersections on the x-axis
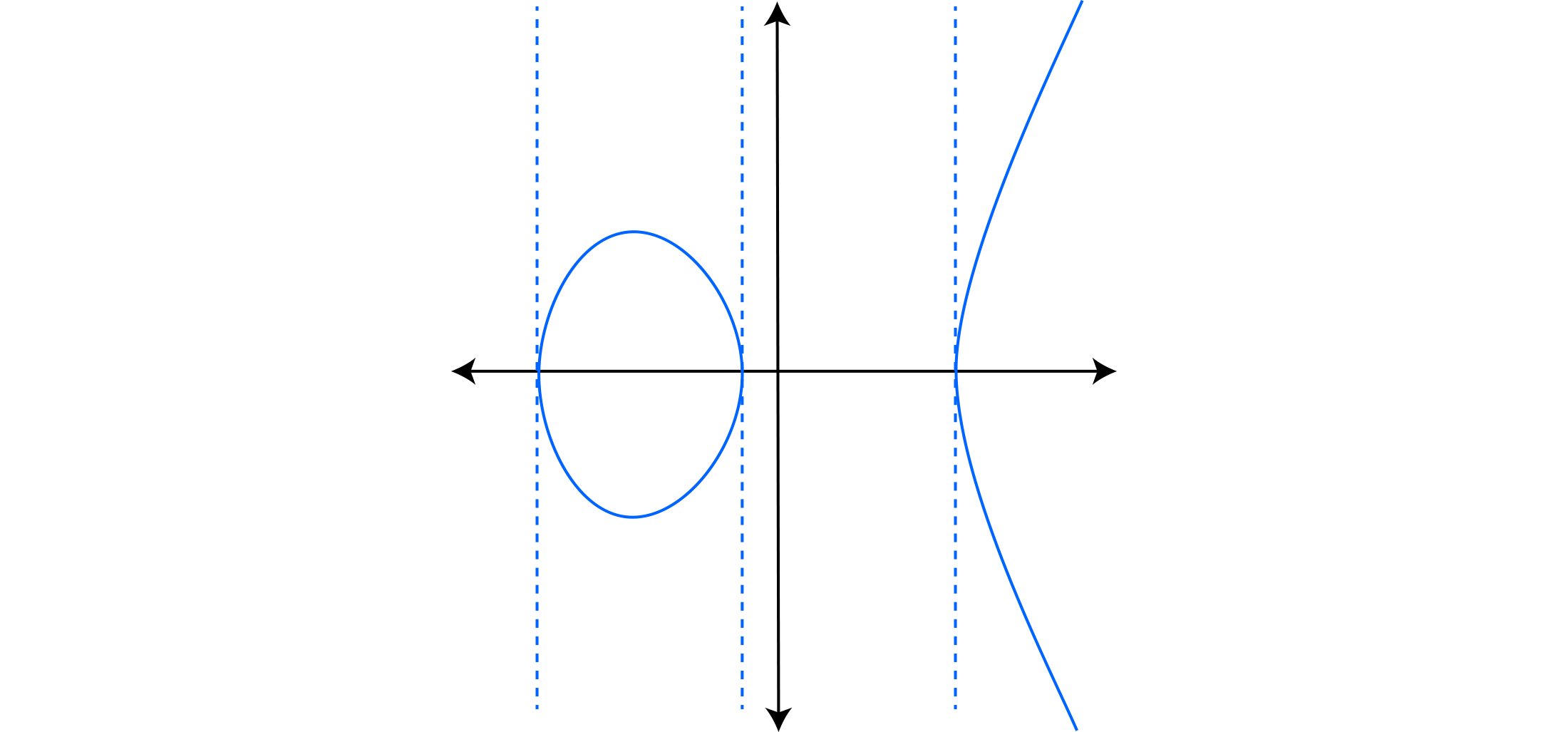
so to find these points we need to solve for
### Field and curve
F = GF(5)
E = EllipticCurve(F, [0, 0, 0, 1, 3]) # y^2 = x^3 + 1*x + 3
### --- 2-torsion criterion (char ≠ 2): points with y=0 and x roots of f(x)=x^3 + x + 3
R.<x> = PolynomialRing(F)
f = x^3 + x + 3
print("Over F_5, f factors as:", f.factor())
### We see only one linear factor (x-1), so only (1,0) is 2-torsion over F_5
P_F5 = E(1,0)
print("Check 2*P_F5 == O?", 2*P_F5 == E(0))
### --- Go to quadratic extension to get full E[2]
K.<u> = GF(5^2) ## quadratic extension
EK = E.change_ring(K)
R2.<x> = PolynomialRing(K)
fK = R2(f)
print("Over F_25, f factors as:", fK.factor())
### Collect all 2-torsion points over F_25: the three roots give (x_i, 0), plus O
roots = [r for (r, mult) in fK.roots()] ## three distinct roots in K (since char!=2 and Δ ≠ 0)
E2 = [EK(0)] + [EK(r, K(0)) for r in roots]
print("E[2] over F_25 has size:", len(E2))
print("E[2] points:")
for Q in E2:
print(" ", Q)
### Sanity: each nonzero 2-torsion point has order 2
print("Orders of nonzero 2-torsion points:")
for Q in E2[1:]:
print(Q.order())
After running the code we see that there are 3 non-trivial 2-torsion points along with the point at infinity in the subgroup.
An isogeny is a non-constant group homomorphism given by rational functions. Such maps are automatically surjective with finite kernel. On short Weierstrass models, after normalizing so that , an isogeny takes the affine form
where the degree is defined as . When is separable, meaning the derivative is not identically zero, the degree equals the size of the kernel: .
Supersingularity is preserved by isogeny:
Let's look at the isogeny from the elliptic curve defined over to itself defined by the multiplication-by-2 map. The isogeny takes every point to its double
### Field and curve
F = GF(5)
E = EllipticCurve(F, [0, 0, 0, 1, 3]) ## y^2 = x^3 + 1*x + 3
### --- Go to quadratic extension
K.<u> = GF(5^2) ## quadratic extension
EK = E.change_ring(K)
Xmap, Ymap = EK.multiplication_by_m(2)
print("x(2P) =", Xmap)
print("y(2P) =", Ymap)
So the map for doubling a point is
The kernel for this isogeny is exactly the 2-torsion subgroup we saw earlier, the cardinality of which was 4 and that is consistent with the degree of our isogeny.
If and are isogenies, their composition
is again an isogeny, and its degree multiplies:
An isomorphism is just an isogeny of degree whose kernel is ; composing an isomorphism with its inverse is the identity. For a general isogeny of degree , there is no inverse in the usual sense. Instead, there exists a unique dual isogeny that "acts like" an inverse up to multiplication-by-:
Thus the composition returns to the same curve and its kernel is the full -torsion:
An isomorphism over is an isogeny of degree 1, taking the form
Isomorphisms preserve the -invariant: if is an isomorphism, then . Over an algebraically closed field, the converse holds: two elliptic curves are isomorphic if and only if their -invariants coincide.
The number of supersingular -invariants in characteristic is
giving approximately such invariants.
In some applications, we know the kernel of a desired isogeny but need to construct the explicit map. Specifically, given an elliptic curve and a finite subgroup , we wish to compute the isogeny whose kernel is precisely .
Vélu's formulas solve this problem. They take as input the coefficients defining the curve and the list of all nonzero points in the subgroup (or simply a generator when is cyclic). From this data, Vélu's formulas produce:
For a cyclic subgroup of order , the resulting isogeny
is separable with . This kernel-first approach is fundamental to isogeny-based cryptography, where parties construct secret isogenies by choosing secret kernel generators.
### Base curve over F_5, then extend to F_{5^2} so E[2] is fully defined
F = GF(5)
E = EllipticCurve(F, [0,0,0,1,3]) ## y^2 = x^3 + x + 3
K.<u> = GF(5^2)
EK = E.change_ring(K)
### E[2] points: roots of x^3 + x + 3 with y=0
R.<x> = PolynomialRing(K)
f = x^3 + x + 3
roots = [r for (r, _) in f.roots()] ## 3 distinct roots in K
E2_pts = [EK(r, K(0)) for r in roots] ## the three nonzero 2-torsion points
### Pass a LIST OF GENERATORS for the kernel subgroup (any two independent E[2] points)
phi2 = EllipticCurveIsogeny(EK, E2_pts[:2]) ## uses Vélu with kernel generated by these points
E2cod = phi2.codomain()
print("deg(phi2) =", phi2.degree()) ## should be 4
### Kernel sanity: all of E[2] (including O) maps to O
for Q in [EK(0)] + E2_pts:
assert phi2(Q) == E2cod(0)
print("Kernel OK (E[2] → O).")
In SageMath the EllipticCurveIsogeny constructor takes as input a starting curve and a point or list of points that generate the kernel and uses Vélu's formulas to construct the isogeny.
SIDH begins with a prime of the form
where and are positive integers chosen such that . All computations are performed over the quadratic extension field .
This prime structure is carefully chosen. For a supersingular curve defined over , the number of -rational points is
and the group structure is
Since , the curve contains points of every order dividing . This enables Alice and Bob to independently traverse their respective isogeny graphs using powers of 2 and 3.
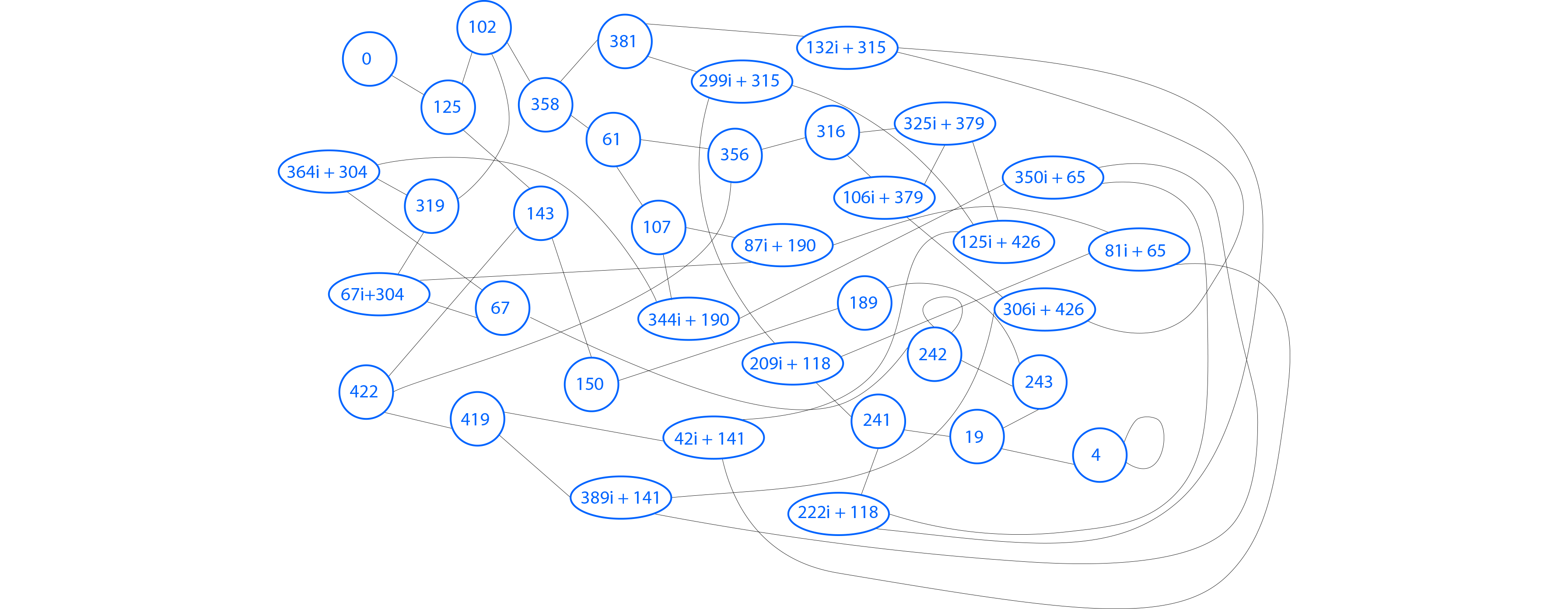
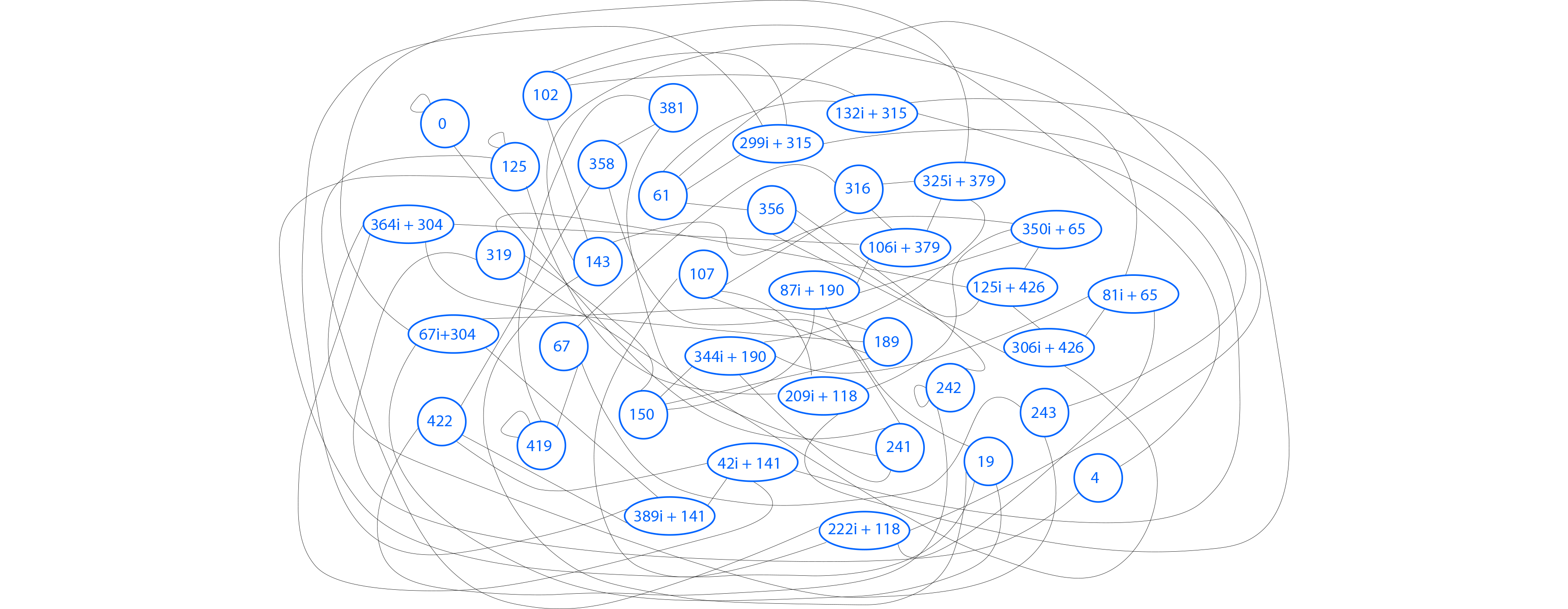
The protocol operates on two supersingular isogeny graphs sharing the same vertex set but with different edge structures.
Vertices represent isomorphism classes of supersingular elliptic curves over , uniquely identified by their -invariants.
Edges are defined by isogenies: for a prime coprime to , an -edge connects vertices and if there exists a separable -isogeny over .
For , the -torsion subgroup has structure
containing exactly cyclic subgroups of order . Each cyclic subgroup determines a unique separable isogeny via Vélu's formulas. Consequently, each vertex in the -isogeny graph has exactly neighbors.
For Alice's 2-isogeny graph, each vertex has 3 outgoing edges (with negligible exceptions). For Bob's 3-isogeny graph, each vertex has 4 outgoing edges.
The protocol requires a fixed supersingular starting curve defined over and two pairs of torsion basis points:
These bases generate the torsion subgroups
Alice's key generation:
Alice selects a secret integer and constructs the kernel generator
The cyclic subgroup has order . Alice computes the isogeny
as a composition of successive degree-2 isogenies, effectively traversing edges in the 2-isogeny graph.
Alice's public key is
The public key includes both the image curve and the images of Bob's torsion basis points under her secret isogeny.
Bob's key generation:
Bob follows the analogous procedure using 3-power isogenies. He selects a secret and constructs
Bob computes the isogeny
as a composition of successive degree-3 isogenies.
Bob's public key is
Alice's computation:
Upon receiving Bob's public key, Alice constructs
using the fact that isogenies are group homomorphisms. The cyclic subgroup equals , the image of Alice's original kernel under Bob's isogeny.
Alice then computes
Bob's computation:
Bob performs the symmetric computation, constructing
so that , and computing
The shared secret:
A fundamental theorem of isogeny theory guarantees a canonical isomorphism
which implies and therefore .
The shared secret is the common -invariant:
Both parties arrive at isomorphic curves and compute the same -invariant. The security of SIDH relies on the computational difficulty of determining the isogeny (or ) from knowledge of and (or ), a problem believed to be hard even for quantum computers.
For our example we choose the prime to be , the starting curve where . Next we fix the basis points for Alice and Bob
Alice generates a secret number and computes the kernel generator point
This point has order 16 which could express a degree 16 isogeny or a composition of 4 degree 2 isogenies. The latter is favorable for computational purposes so Alice computes the 4 "hops" in the isogeny graph using Vélu's formulas at each step and lands on the image curve which will be her public key (encoded by its Montgomery parameter) along with Bob's basis points under the same secret isogeny
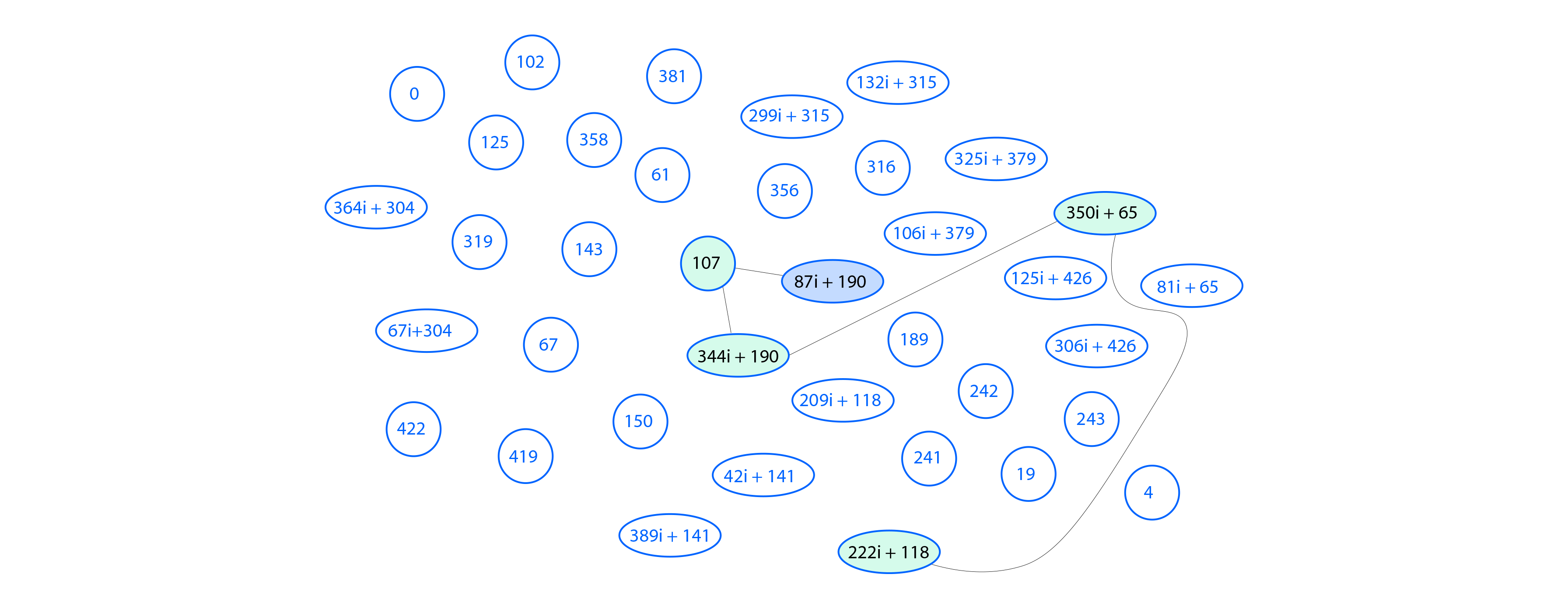
The below image shows the "hops" Alice takes on the -invariants of her respective curves.
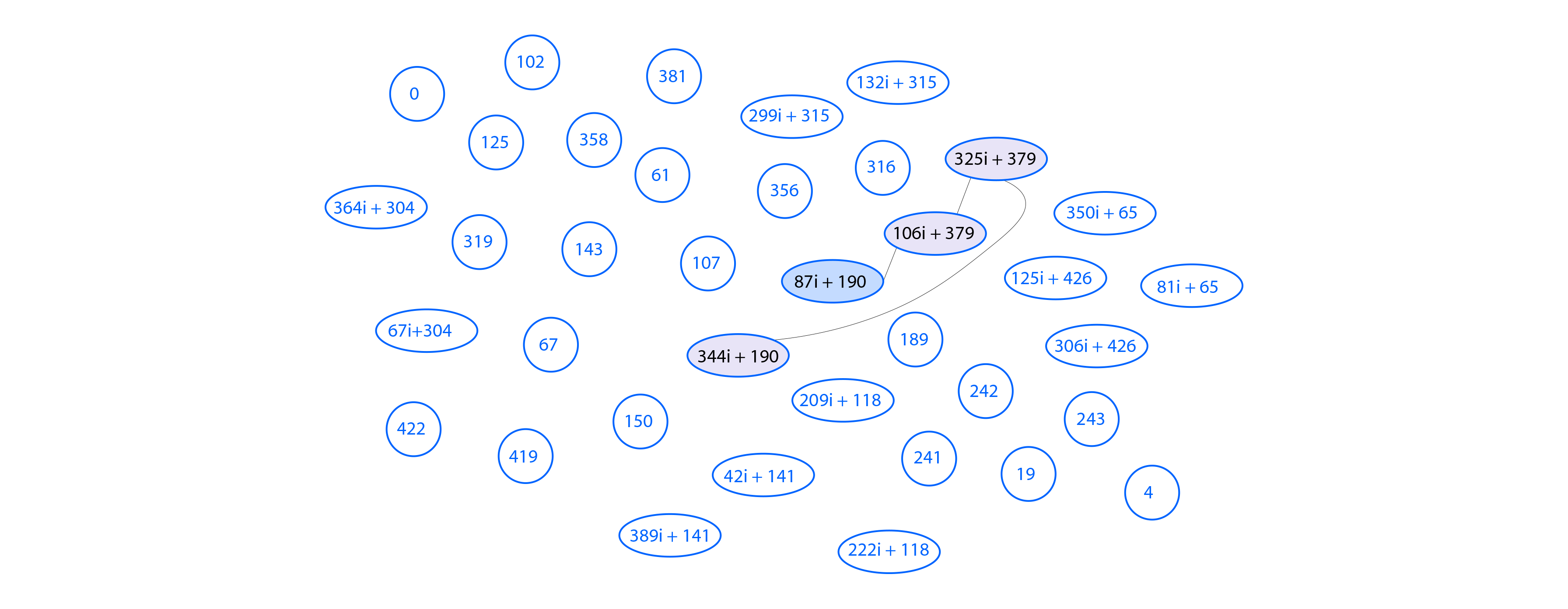
Bob also chooses a secret parameter and computes the corresponding generator point
which has order 27 meaning Bob can interpret it as a composition of 3 degree 3 isogenies. His public key is also the resulting curve and Alice's basis points under his secret isogeny
Now for the shared secret computation, Alice takes Bob's codomain curve from his public key as the starting point then calculates the kernel using the image of her basis points that Bob provided
and just like before computes the image curve using the kernel generated by .
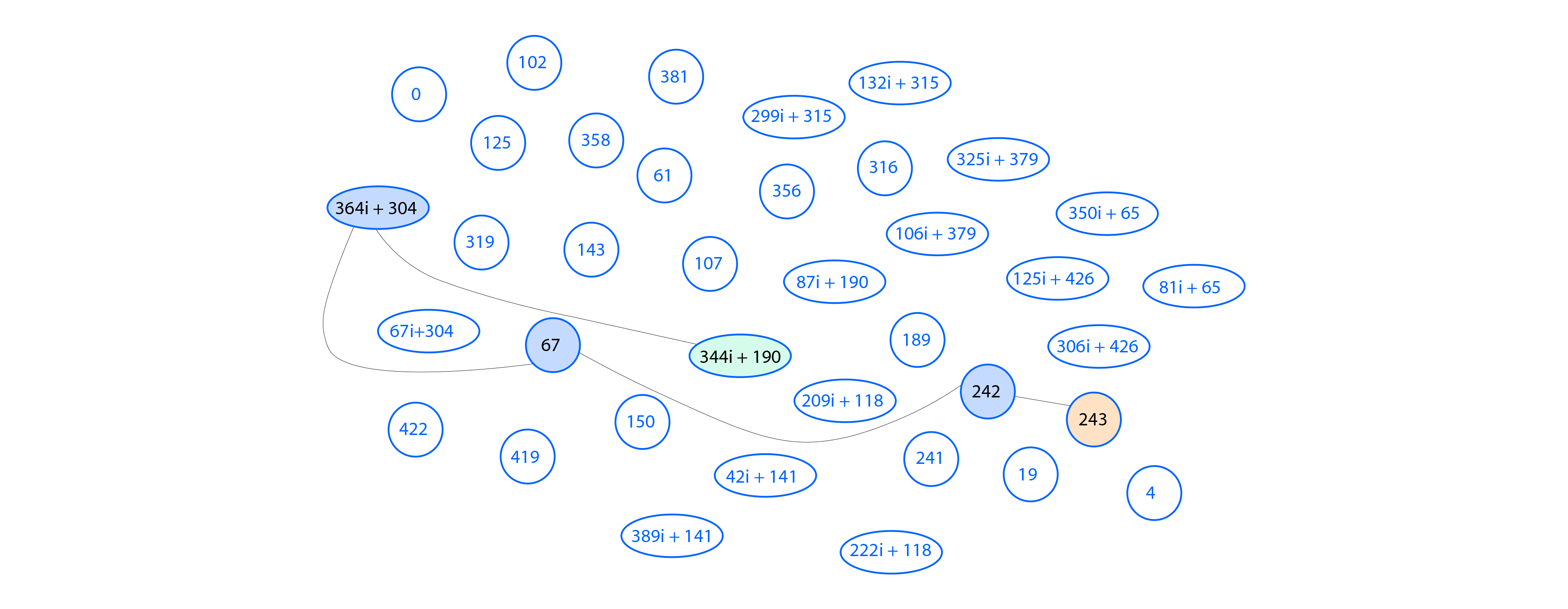
Bob goes through the same steps and ends up with
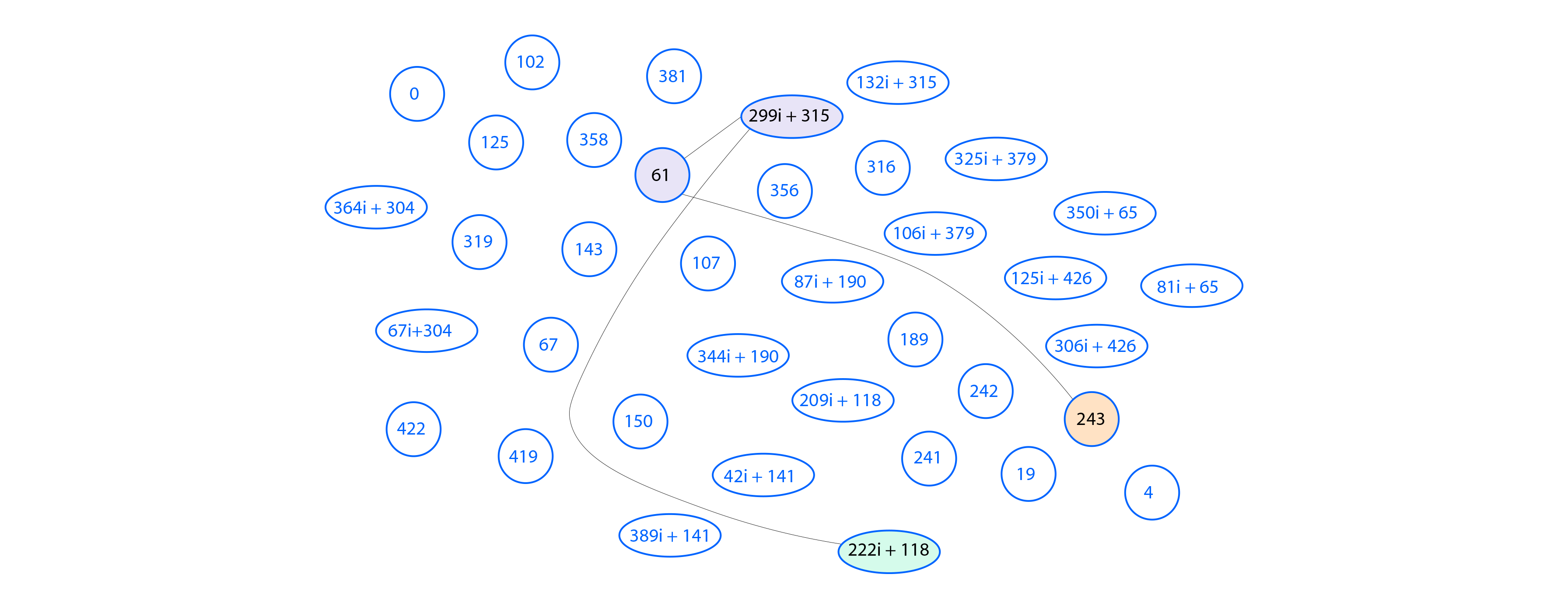
After these steps they both land on the node with -invariant = 243, and this shared secret can be used to derive cryptographic keys.
The security of SIDH rests on the hardness of the following problem: given two supersingular curves and , recover the secret cyclic kernel that defines the separable isogeny of degree .
When walking along a 3-isogeny path, there are 4 degree-3 choices at the first step. After ruling out the dual edge (which returns to the previous curve), there remain 3 choices at each subsequent step. If an oracle existed that could test whether a proposed next 3-isogeny lies on the secret path, one could recover the entire path by testing the 3 candidates at each level.
The Castryck-Decru attack constructs such an oracle by lifting from elliptic curves (dimension 1) to principally polarized abelian surfaces (dimension 2), where testing whether the surface is a Jacobian versus a product of elliptic curves provides the required signal.
The core idea is based on a theorem by Kani relating isogeny diamonds to products of elliptic curves.
The attack constructs such a diamond in dimension 2 by:
The key insight is that the final surface is a product of elliptic curves if and only if the candidate 3-isogeny lies on Bob's secret path. This follows from Kani's theorem combined with the specific structure of the diamond.
Since a random principally polarized abelian surface of dimension 2 is a Jacobian with probability approximately , while a product occurs with probability roughly , this test reliably distinguishes correct from incorrect candidates.
The attack recovers Bob's secret isogeny of degree by determining it one step at a time. Since Bob computes his isogeny as a composition of successive degree-3 isogenies, the attacker recovers each individual 3-isogeny in the chain using the dimension-2 oracle.
Bob's secret isogeny is a composition of degree-3 isogenies:
The attack recovers these isogenies sequentially. At step , having already recovered , the attacker knows the current curve and seeks to determine .
Step : Recovering the next 3-isogeny
Identify the candidate edges:
From curve , there are 4 outgoing 3-isogenies. However, one of these is the dual of the incoming isogeny , which can be ruled out (except at the first step). This leaves 3 candidate edges to test.
Construct the auxiliary isogeny:
The oracle requires an auxiliary isogeny of degree . Assuming has a known endomorphism (such as satisfying ), and assuming can be written as , construct the degree- endomorphism:
Evaluate on the generators to obtain:
Test each candidate:
For each of the 3 candidate isogenies :
a. Push the torsion through the candidate path:
Compute the images of the generators under the composition of the recovered path and the candidate:
b. Form the diamond kernel:
Consider the -subgroup of generated by:
This subgroup always defines a -isogeny.
c. Glue into dimension 2:
The first step of this -isogeny is a gluing map that takes the product of elliptic curves to the Jacobian of a genus-2 curve .
d. Compute the Richelot chain:
Compose successive Richelot -isogenies:
e. Test for splitting:
After the chain of Richelot isogenies, check whether the final -isogeny splits—that is, whether its codomain is a product of two elliptic curves rather than a Jacobian of a genus-2 curve.
The test is straightforward: in the Richelot formulas, a certain determinant appears. The codomain is a product if and only if .
f. Apply Kani's theorem:
Advance to the next step:
Once the unique candidate that makes the diamond split is identified, set and update the current curve to . Proceed to step .
After iterations, the complete chain has been recovered. This determines Bob's secret isogeny and its kernel .
In terms of Bob's secret key: if Bob's private key is the integer such that , then the attack recovers one base-3 digit at a time.
A crucial aspect of the attack is its reliance on the torsion point information in SIDH public keys. Recall that Alice's public key includes not just her image curve , but also the images of Bob's torsion basis.
This auxiliary information is essential for SIDH's key exchange mechanism—without it, Bob cannot compute the shared secret. However, it also provides the attacker with the ability to:
Without this torsion point information, the attack does not apply. This observation led to the development of SIDH variants that attempt to hide or obfuscate the torsion point images, though designing secure and efficient alternatives remains an active area of research.
The simplified description above assumes:
In the more general attack:
Regardless of these variations, the core logic remains the same: use the dimension-2 oracle to test candidate edges one step at a time until the entire secret path is recovered.
The Castryck-Decru attack, published in July 2022, completely broke SIDH security. Within hours of the preprint appearing on ePrint, the attack was implemented and verified against SIDH implementations. The attack applies to all standard SIDH parameter sets and cannot be mitigated by simply increasing key sizes.
This development eliminated SIDH as a candidate for post-quantum cryptography standardization. The attack highlighted the danger of including auxiliary information (torsion point images) in isogeny-based protocols, spurring research into alternative designs that either avoid this information or protect it through other means.
This write-up closely follows and synthesizes material from the three references listed below.
The author gratefully acknowledges these works for their clear notation, precise statements of facts, and concrete algorithmic descriptions, which this post reproduces and condenses for a cohesive, technically faithful walkthrough of SIDH and its break.