FHE
Aug 26, 2025
MHE from RLWE: When MPC Meets Homomorphic Encryption
Discover how Multiparty Homomorphic Encryption (MHE) overcomes the communication overhead and synchronization limits of Secure Multiparty Co...
FHE
Aug 13, 2025

Fully homomorphic encryption (FHE) promises to unlock computation on encrypted data, but practical schemes face fundamental limitations that constrain their real-world applicability. The BFV (Brakerski-Fan-Vercauteren) scheme, one of the most widely used FHE constructions, exemplifies a critical trade-off that has shaped the field: you can either pack large amounts of data per ciphertext or perform deep computations, but not both.
This limitation isn't merely a technical inconvenience, it fundamentally constrains the types of applications FHE can serve. Machine learning inference on encrypted data, secure database queries, and privacy-preserving analytics all demand both high data throughput and substantial computational depth. Yet classical BFV forces practitioners into an uncomfortable choice between these requirements.
Recent advances in generalized BFV schemes offer a path beyond this trade-off. By replacing the traditional integer plaintext modulus with carefully chosen polynomial quotients, these constructions can maintain large plaintext spaces while achieving multiplicative depths that scale with the ciphertext modulus rather than being inversely related to the plaintext size.
This article explores how the quotient-by- construction breaks free from classical BFV's fundamental limitations, examining both the mathematical foundations and practical implications of this approach.
Let be the cyclotomic index. The classical BFV scheme operates over:
The core operations follow a familiar pattern:
KeyGen: Pick , , ; set . Public key ; secret key .
Encrypt :
Decrypt :
The core limitation of classical BFV stems from its noise growth behavior. Increasing the plaintext modulus to pack more data per ciphertext comes at a steep cost: the maximum multiplicative depth is roughly bounded by , so larger plaintext spaces directly reduce computational capacity. To maintain depth while increasing , we must grow proportionally, but larger ciphertext moduli make every operation more expensive: more memory for keys, slower NTTs for polynomial arithmetic, and costlier key-switching.
The result is an unavoidable choice: high-throughput applications with large sacrifice multiplicative depth, while deep computations are constrained to small plaintext spaces.
For the foundational BFV construction and security analysis, see "Somewhat Practical Fully Homomorphic Encryption"
The breakthrough comes from recognizing that the plaintext modulus need not be an integer. Instead of working modulo , we can construct plaintext rings using polynomial quotients of the form , where is a small integer and divides certain structural parameters of the cyclotomic polynomial.
This seemingly simple change has profound implications for noise growth and multiplicative depth, offering a path to escape classical BFV's fundamental limitations.
We keep the ciphertext ring exactly as in classical BFV, using one NTT-friendly prime:
For the plaintext ring, we introduce a binomial relation. Write and let:
We leverage a classical identity for cyclotomic polynomials:
(the product of distinct primes dividing ); equivalently is the largest square-free divisor of .
Euler’s totient .
Möbius function ; if is divisible by a square; if is a product of distinct primes.
-th cyclotomic polynomial the unique monic polynomial whose roots are the primitive -th roots of unity. It has degree and integer coefficients.
Theorem If arithmetic functions satisfy then
Proof. Assume . Consider Insert the definition of : Re-index: each pair with appears once; write with . But for and for . Hence all exponents vanish except when , giving .
Theorem For every ,
Proof. A primitive -th root is also a -th root whenever , so is a root of the product on the right. Both polynomials are monic of degree , hence equal.
Theorem For and ,
Proof. Apply the first theorem to the arithmetic function .
Statement. For every ,
Proof. Write and (so and ).
We have Because whenever is not square-free, the only divisors that contribute are square-free, i.e. . Replace by :
Now compare with the formula of the 3rd theorem for , evaluated at : Hence , as claimed.
To construct our new plaintext ring, we reduce modulo by substituting . Because , this substitution yields a constant:
Hence the joint ideal collapses to , giving us:
Lemma: Let and . Choose with , and set . For , assume is prime and . Write .
Then splits over into distinct irreducible factors of degree . The Galois group is .
The crucial advantage of generalized BFV emerges from how we represent plaintexts in the new ring. When encrypting , we use the relation to find a representation with small coefficients:
This is possible because the binomial relation lets us "carry" large powers into exponential form, keeping all coefficients bounded by .
After multiplications, the worst-case coefficient grows like , giving a depth bound:
Since (we choose to be small), this dramatically improves upon classical BFV's bound. The binomial modulus enables far greater multiplicative depth without enlarging the ciphertext prime .
For a comprehensive introduction to SIMD operations in FHE, see our previous post "One Ciphertext, Many Messages: SIMD operations in FHE".
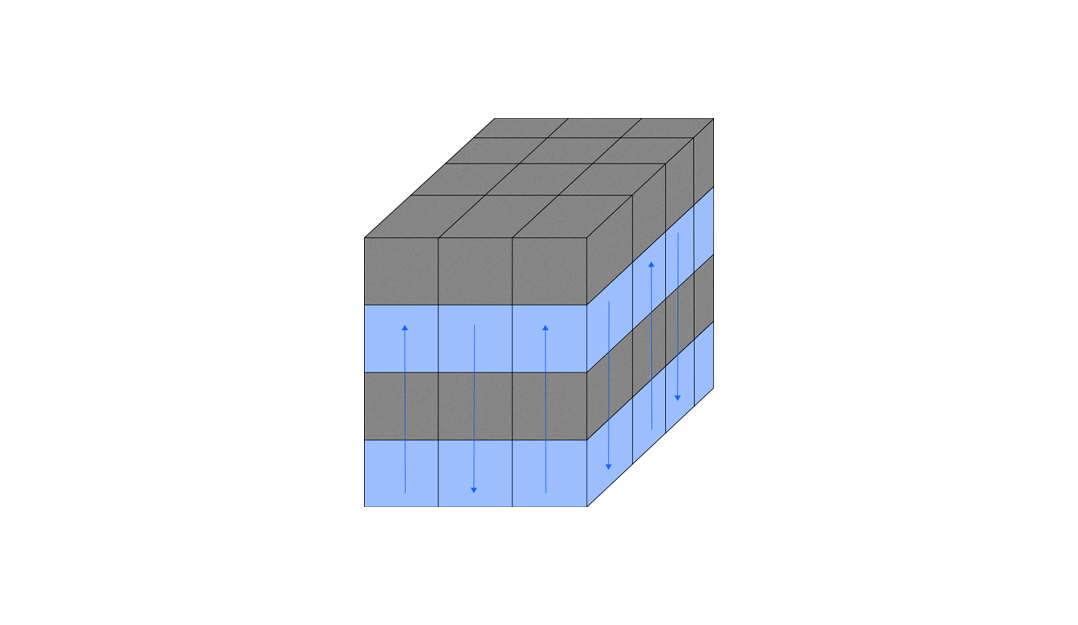
Classical BFV enjoys independent SIMD slots:
Adding the binomial relation fundamentally changes this structure. We can understand the effect by thinking slot-wise:
For each slot, we "apply the quotient by " locally:
This creates two possibilities:
| Condition on | Resulting ideal | Effect on the slot |
|---|---|---|
| the zero ideal | The slot remains unchanged | |
| the whole ring | The slot is completely eliminated |
Consequently, a slot survives if and only if its root of unity is a -th root of . Counting these roots yields exactly surviving slots, each operating over .
The relationship between generalized and classical BFV can be understood through the auxiliary prime .
Since lies in the ideal , we can express it as:
where and are integer polynomials. Reducing modulo , this becomes:
where is reduced modulo . This gives us the fundamental relationship: as ideals in .
In the quotient ring , we have , which means:
Since each slot behaves like a field, exactly one of or must be zero in each slot:
| Slot type | Condition | Ideal |
|---|---|---|
| -slot | , | |
| -slot | , |
By the Chinese Remainder Theorem:
Generalized BFV makes its crucial choice here: it keeps only the block, eliminating all -slots and preserving only the -slots where .
Some applications, particularly bootstrapping, require a plaintext space defined modulo a prime power rather than just a prime .
Our binomial ring construction adapts seamlessly to this requirement. Hensel's lemma allows us to lift the factorization:
to every power without changing the CRT slot structure.
We transition from field-level slots to Galois rings:
This preserves the same SIMD lanes while providing coefficients modulo . The Hensel lift provides the -adic precision that bootstrapping requires, yet introduces no additional noise. After the ciphertext is refreshed, we can reduce back to modulus and continue the GBFV computation with all its low-noise advantages intact.
The primary challenge with bootstrapping generalized BFV stems from its restricted structure: GBFV operates in a subring , which severely limits the automorphisms available for bootstrapping.
Standard BFV bootstrapping relies on access to the complete automorphism group:
These rotations are essential for:
However, in GBFV's quotient ring where , only rotations that preserve the ideal remain valid. This dramatically reduces the available automorphism group to:
We can only rotate within the block, we cannot access the rotations that would move between the and components of the full BFV ring.
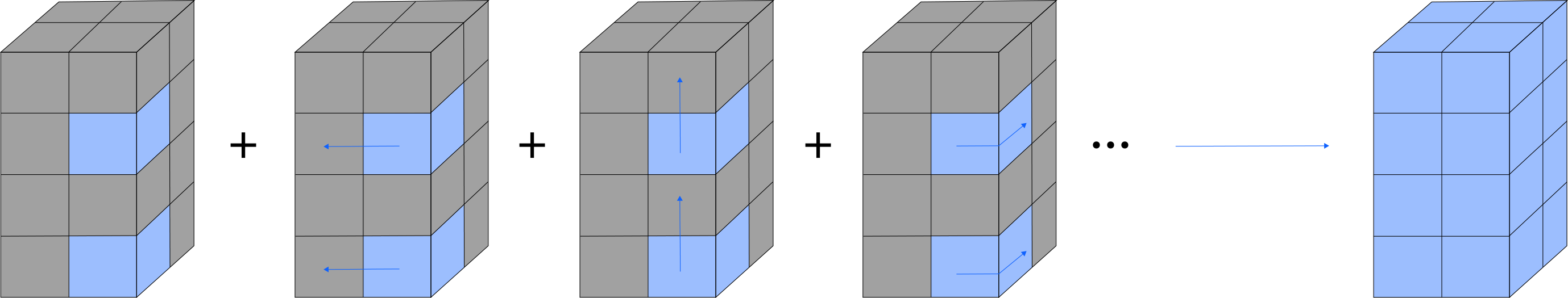
The key insight is to temporarily lift GBFV ciphertexts back to the full BFV ring , where all necessary rotations become available.
Rather than bootstrapping a single GBFV ciphertext (which would waste the slots), we pack multiple GBFV ciphertexts into one BFV ciphertext. This ensures that every BFV slot contains meaningful data from some GBFV ciphertext, maximizing the efficiency of the bootstrap operation.
With all slots filled, we run the standard BFV bootstrapping procedure. The bootstrap operation is agnostic to our packing scheme, it simply refreshes all slots in the full ring, where all required rotations are available.
To recover individual GBFV ciphertexts:
The projection naturally eliminates the block while preserving the block. By performing appropriate rotations during unpacking, we can retrieve any of the GBFV ciphertexts that were packed into the original BFV ciphertext.
This approach transforms GBFV's fundamental limitation, its restricted automorphism group, into an advantage by enabling batch bootstrapping of multiple ciphertexts simultaneously.
Let's work through a concrete example to illustrate the theory in practice.
We work in:
There is a primitive -th root since and .
The four BFV slots correspond to evaluations at for :
Equivalently, we have the complete factorization:
To determine which slots survive after quotienting by , we use the rigorous slot-wise analysis: the quotient by eliminates exactly those BFV slots where and preserves those where .
Step 1: Reduce and evaluate at the four roots :
Step 2: Under the Chinese Remainder Theorem, the principal ideal generated by corresponds to:
Step 3: In a field , we have if and if . Therefore:
So overall:
Step 4: Taking the quotient coordinate-wise:
This shows that slots 1 and 3 survive (corresponding to roots and ), while slots 2 and 4 are eliminated.
Classical BFV automorphisms are for .
After quotienting by , only those automorphisms that preserve the -block remain valid. For , the surviving subgroup is:
Here , so .
Indeed, swaps the two surviving slots, while and would send surviving slots to eliminated positions (making them invalid in ).
m = 8
p = 17
k = 2
b = 4
Fp = GF(p) # the base field F_p
R.<x> = Fp[] # polynomial ring F_p[x]
Phi = cyclotomic_polynomial(m).change_ring(Fp) # X^4 + 1 in F_p[x]
Rp = R.quotient(Phi, 'Xbar') # Rp = F_p[x]/(Phi_m)
Xbar = Rp.gen()
### Find a primitive m-th root of unity α in F_p (requires m | p-1)
g = Fp.multiplicative_generator() # generator of F_p^*
alpha = g^((p - 1)//m)
assert alpha.multiplicative_order() == m, "No primitive m-th root in F_p; need extension field."
print("\nFound primitive %d-th root α in F_%d:" % (m, p), int(alpha))
### Classical BFV slot exponents: units mod m
slot_exps = [j for j in range(1, m) if gcd(j, m) == 1]
alphas = [alpha^e for e in slot_exps]
print("\nBFV slot points α^j for j in (Z/%dZ)^* = %s:" % (m, slot_exps),
[int(a) for a in alphas])
### Factorization over F_p (use Phi for clarity)
print("\nFactorization of Phi_%d(X) over F_%d:" % (m, p))
fac = Phi.factor()
print(" ", fac)
### Extract linear roots from the factorization and verify they match {alpha^j}
roots = []
for f, e in fac: # linear factors f = x - r
if f.degree() != 1:
raise RuntimeError("Phi_m did not split linearly over F_p; need extension field.")
r = -f[0] # r = -constant term
roots.append(r)
### Check sets match (as multisets)
assert set(roots) == set(alphas), "Factorization roots != {alpha^j : j∈(Z/mZ)^*}"
print("Roots (some order):", [int(r) for r in roots])
### Survival under t(X) = X^k - b (here k=2, b=4)
t = x^k - b
t_vals = [t(a) for a in alphas]
survivor_mask = [(tv == Fp(0)) for tv in t_vals] # survive iff t(α)=0
print("\nEvaluate t(X)=X^%d-%d at slot points:" % (k, b))
for j, a, tv in zip(slot_exps, alphas, t_vals):
status = "SURVIVES" if tv == 0 else "KILLED"
print(f" t(α^{j}) = t({int(a)}) = {int(tv):2d} -> {status}")
Generalized BFV with polynomial quotients represents a significant advance in practical fully homomorphic encryption. By replacing the classical integer plaintext modulus with carefully chosen binomial relations , we escape the fundamental trade-off between data packing and multiplicative depth that has constrained classical BFV.
The key insights are:
These advances open new possibilities for applications requiring both high throughput and deep computation, bringing FHE closer to practical deployment in privacy-preserving machine learning, secure database operations, and encrypted analytics.
The generalized BFV construction demonstrates that fundamental limitations in cryptographic schemes can sometimes be overcome not by abandoning existing frameworks, but by recognizing and exploiting the deeper algebraic structures they contain.
This work builds upon the foundational research presented in two key papers that introduced and developed the generalized BFV framework. We gratefully acknowledge the contributions of the authors of "Fully Homomorphic Encryption for Cyclotomic Prime Moduli" and "MatriGear: Accelerating Authenticated Matrix Triple Generation with Scalable Prime Fields via Optimized HE Packing". Their innovative approach to polynomial quotient constructions and rigorous analysis of noise behavior provided the theoretical foundation that made this exposition possible. The mathematical insights and practical considerations presented in these works have significantly advanced the field of fully homomorphic encryption and enabled new possibilities for privacy-preserving computation.