Security
Dec 16, 2025
Attacks on Threshold Schemes: Part 2
Deep dive into protocol-level vulnerabilities in threshold signature schemes: MtA oracle attacks, reshare synchronization flaws, determinist...
Security
Aug 31, 2025

The explosion of decentralized finance (DeFi) and permissionless token creation has unlocked new financial primitives - but it has also introduced unprecedented risk for users. Every day, thousands of new tokens are deployed across EVM-compatible blockchains, many of which are designed not as innovative projects, but as vehicles for fraud.
According to the 2025 Chainalysis Crypto Crime Report, over $9.9 billion in on-chain value was lost to scams in 2024, with fraudulent tokens comprising one of the most pervasive vectors. These schemes target everyday traders through DEX listings, viral hype campaigns, and social engineering.
The data is alarming:
The token scam landscape has matured into a professionalized threat ecosystem, often powered by scam-as-a-service infrastructure, AI-generated deception, and increasingly complex smart contract obfuscation.
Smart contracts define the behavior of tokens. Malicious actors routinely exploit this by embedding functionality into code that looks legitimate on the surface, but can be abused for illicit action. Some of the most common mechanisms include:
| Risk Type | Description |
|---|---|
| Honeypots | Preventing users from selling after purchase. |
| Mintable Tokens | Enabling unlimited supply inflation to dilute value. |
| Transfer Pausing | Allowing owners to arbitrarily freeze trading. |
| Blacklists | Selectively blocking addresses from transacting. |
| Ownership Retention | Centralized privileges to change token logic or execute backdoors. |
| External Calls in Transfers | Executing arbitrary external code during transfers. |
| Balance Manipulation | Altering token balances via non-standard or deceptive methods. |
These features are not always visible through public token explorers or simple scanners. Even experienced users may miss them without in-depth contract analysis.
| Category | Estimated Scam Risk | Description |
|---|---|---|
| All Token Launches | 35–40% | Average across all new tokens deployed, including memecoins, DeFi, utility tokens, and presales. Roughly 1 in 3 tokens turns out to be a scam. |
| Meme / Low-Cap Tokens | 80–95% | High-risk tokens with no real utility, often launched by anonymous teams. Most rely on hype, trend-jacking, and are short-lived. |
| Audited / Top 100 Tokens | <5% | Established tokens with public teams, strong liquidity, and security audits. Rarely malicious but still subject to market risk. |
| Tokens Launched via Presale (No Audit / Doxxing) | 90%+ | These tokens collect investor funds upfront without transparency or audit. Most vanish post-sale or rug-pull after launch. |
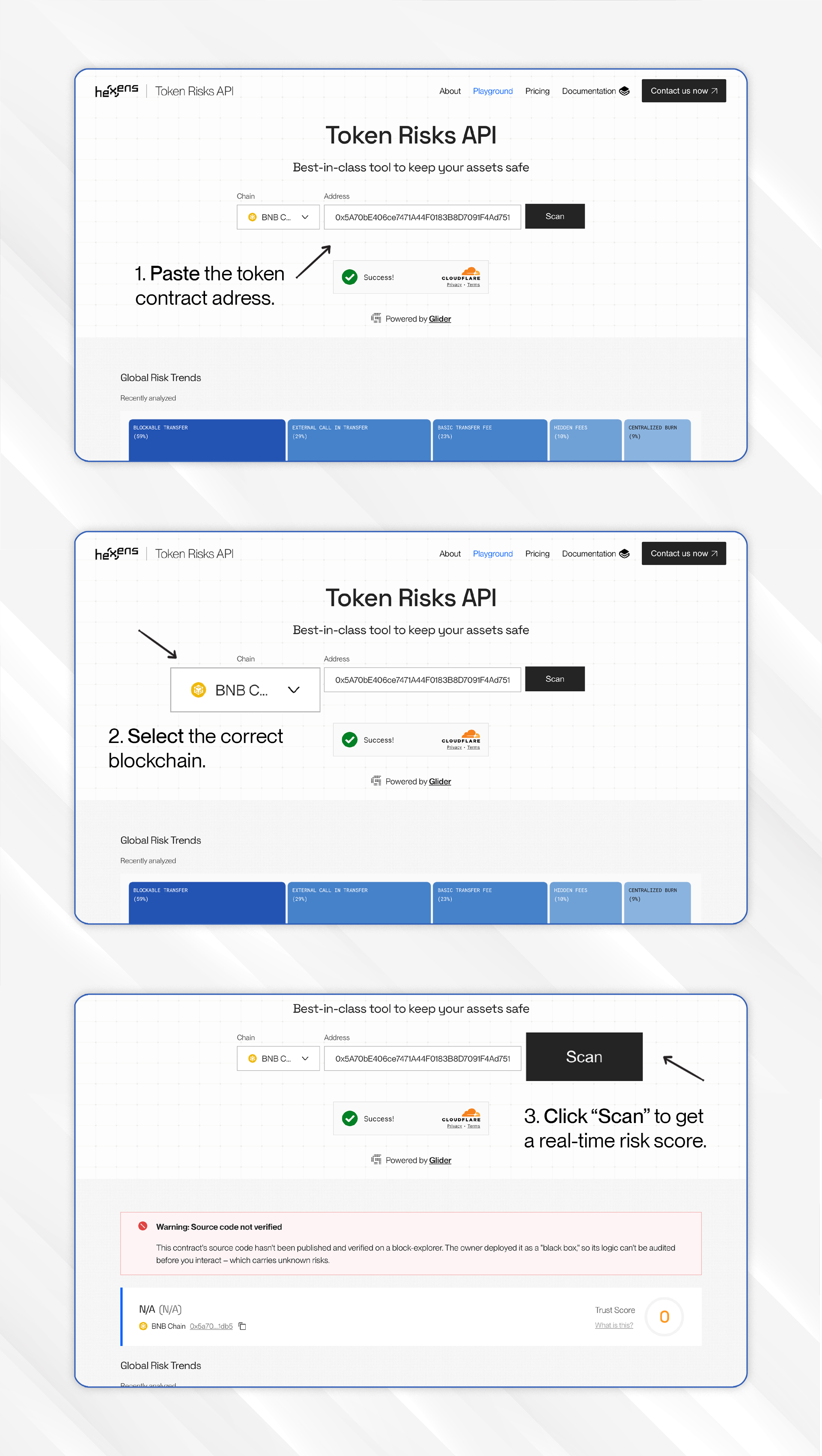
Token Risks API is a real-time, on-chain token security scanner designed to detect 20+ critical threat vectors embedded in ERC20 token contracts. It enables traders, wallets, bots, and DeFi platforms to conduct comprehensive security assessments before interacting with a token.
Each risk is clearly labeled with severity and a contextual explanation, enabling safe decision-making even for non-technical users.
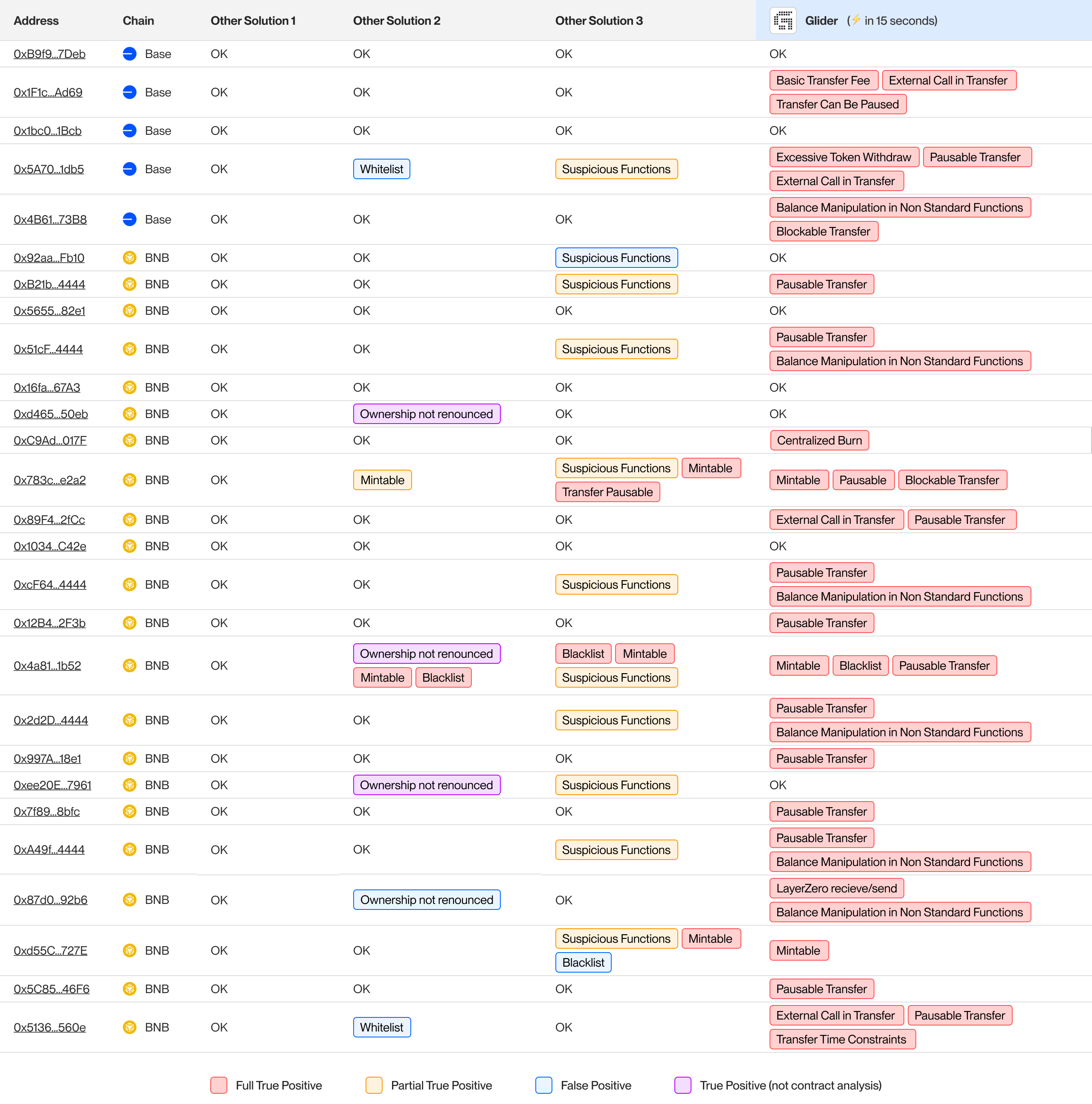
In a recent comparative benchmark of 30 token contracts - including real-world scams - Glider was tested alongside common tools such as TokenSniffer, GoPlus, and QuickIntel.
Results:
Check any token’s scam risk in seconds:
You’ll instantly see:
Perfect for traders, auditors, and anyone vetting tokens before investing.
If you trade without checking a token’s contract, it’s not a matter of if you’ll get scammed - it’s WHEN! With 74,000+ malicious tokens launched in 2024 and $9.9 billion lost to scams, the odds aren’t in your favor.
What makes Token Risks API different is that it isn’t built on surface-level patterns or guesswork. It’s a purpose-built system designed from the ground up to detect real, on-chain threats. It does the job others try to do, but with the depth and precision they were never built for.
In an environment where the cost of a single mistake is often total loss, real-time security analysis isn’t a luxury, it’s essential.
Try the API → Token Risks API