Security
Dec 16, 2025
Attacks on Threshold Schemes: Part 2
Deep dive into protocol-level vulnerabilities in threshold signature schemes: MtA oracle attacks, reshare synchronization flaws, determinist...
Security
Jun 16, 2025

Groups, Cyclic Structure and Lagrange’s Theorem
Cosets and Lagrange’s Theorem
Elliptic Curves over Finite Fields
Fields and Finite Fields
The Curve Equation
Group Law
Base Field vs Scalar Field
Elliptic Curves in Zero-Knowledge Proof Systems
Pairing-Based SNARKs
BN254 and Missing Range Check Exploit
Baby-Jubjub and Subgroup Range Check Attack
Conclusion
Before diving into missing range check attacks in cryptographic circuits, it’s essential to understand what groups are, how their size (order) behaves, and why that matters.
A group is a set with a binary operation (e.g., addition or multiplication) that satisfies the following properties:
A subset is called a subgroup if it is itself a group under the operation inherited from .
The order of a group , denoted , is the number of elements in the group. The order may also be infinite if the group has infinitely many elements.
The order of an element is the smallest positive integer such that , where is the identity element of the group. If no such exists, we say that the order of is infinite.
A generating set (or generator set) of a group is a subset such that every element of can be written as a finite product of elements from and their inverses.
That is, for every , there exists a sequence of indices and exponents such that:
The group generated by is denoted:
If a group has a generating set consisting of a single element , that is , we say that is cyclic.
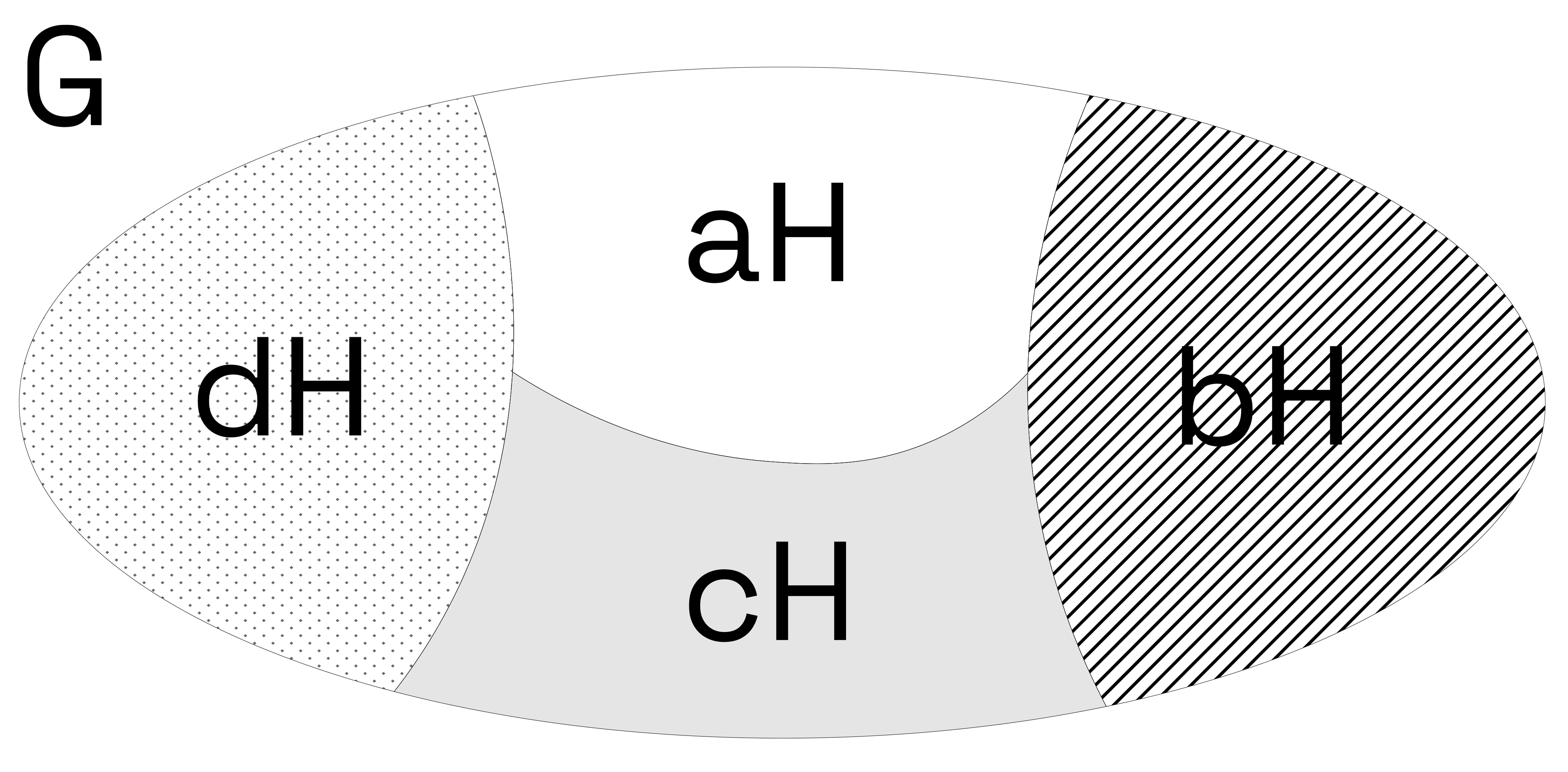
Let be a group and let be a subgroup.
Given an element , the left coset of with respect to is the set:
Similarly, the right coset of with respect to is:
In general, left and right cosets are different unless is a normal subgroup (a concept we will not require here).
One of the key properties of cosets is that the set of all left cosets of in forms a partition of :
That is, for all , either or .
We denote the set of all left cosets of in as:
The number of distinct left cosets is called the index of in , denoted .
All left cosets of a subgroup have the same size as . In fact, for any , the map:
is a bijection (a one-to-one and onto function).
This means that each coset contains exactly elements, and no two cosets overlap. This bijective correspondence is central to the proof of Lagrange’s Theorem, which we will state and prove next.
Let be a finite group and let be a subgroup. Then:
where denotes the number of (left) cosets of in .
Since is a subgroup of , we can form the set of left cosets of in :
We now observe the following facts:
Disjoint Union: The cosets of form a partition of . That is, every element of belongs to exactly one coset. So we can write:
for some representatives .
Equal Size of Cosets: Each left coset has the same number of elements as . This follows from the fact that the map given by is a bijection.
Cardinality Calculation: Since there are disjoint cosets, each of size , and their union gives all of , it follows that:
Let be a finite group with order , and let . Consider the cyclic subgroup generated by , denoted .
Let , which is by definition the order of the element .
Since is a subgroup of , Lagrange's Theorem tells us that the order of any subgroup divides the order of the group. Therefore:
In other words the order of any element divides the order of the group.
Elliptic curves are central objects in modern cryptography. For our purposes, we are interested in elliptic curves defined over finite fields, especially in how they form abelian groups whose structure is relevant to cryptographic protocols — and to attacks.
Before we define elliptic curves, we need to understand the algebraic structure they’re defined over: fields.
A field is a set equipped with two operations:
that satisfy the following properties:
Well-known examples of infinite fields include the rational numbers , real numbers , and complex numbers .
A finite field (or Galois field) is a field with finitely many elements. The most common finite fields are:
In cryptography, we usually work with where is a large prime. Arithmetic in such a field is done modulo :
Finite fields are crucial in elliptic curve cryptography and SNARKs, because they give us a structured but bounded space to compute in — ideal for circuits and modular arithmetic.
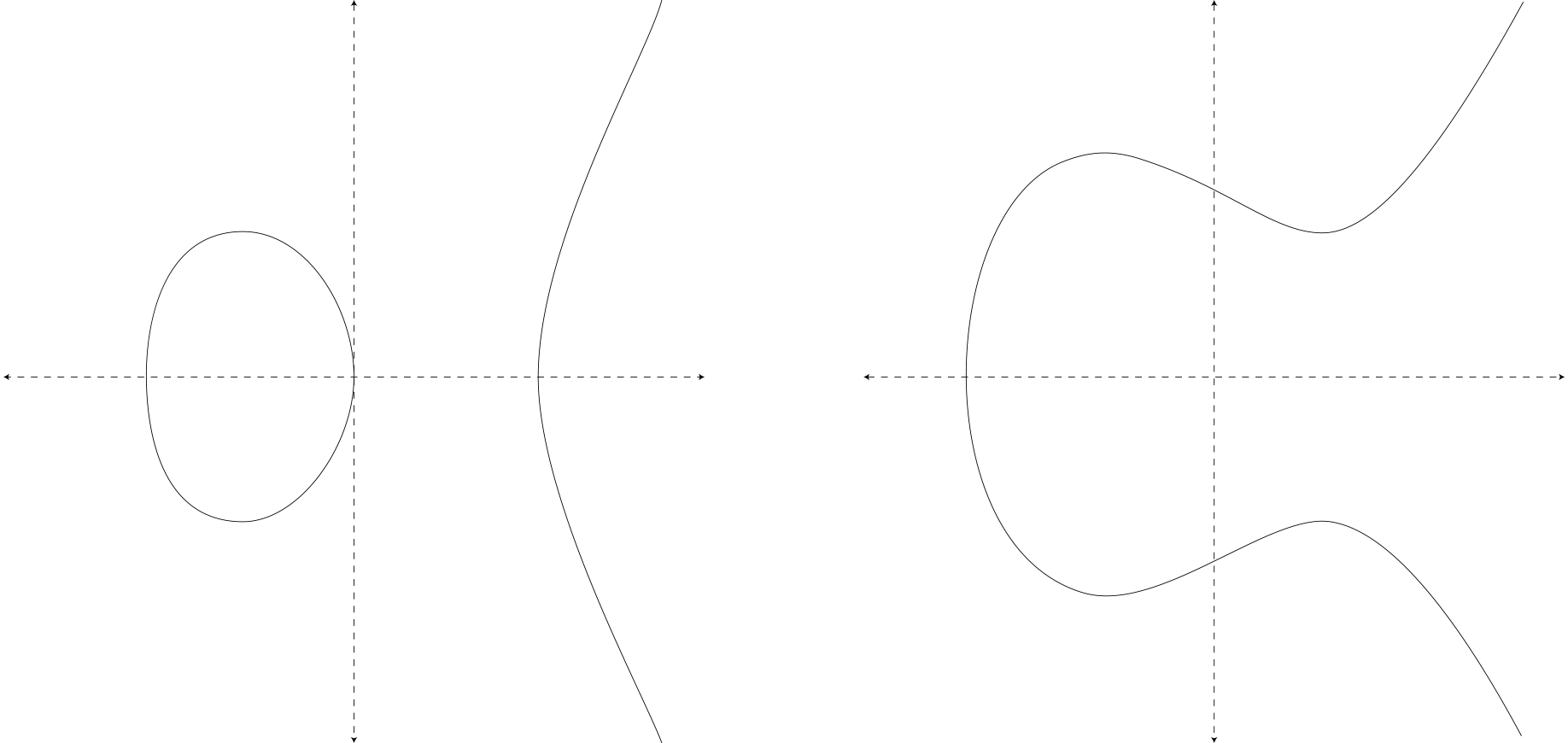
Let be a finite field with elements (typically for some prime , or for small ). An elliptic curve over is the set of solutions to the equation:
where , and the curve is non-singular, meaning:
This condition ensures the curve is smooth and has no cusps or self-intersections.
We also include a special point called the point at infinity, denoted , which acts as the identity element in the group.
The points on an elliptic curve , along with , form an abelian group under a geometric addition law:
The details of the addition formulas are not important here — only the fact that the group law is well-defined, efficiently computable, and gives the set of curve points the structure of a group.
When an elliptic curve is defined over a finite field , the set of its points forms a finite cyclic abelian group.
This means there exists a point such that repeatedly adding to itself generates all of the points on the curve. That is:
for some prime , where and is the order of the elliptic curve group.
This operation — writing any point as a multiple of a generator — is known as scalar multiplication, and the scalars live in a finite field of size .
This brings us to the distinction between two fields in elliptic curve cryptography:
So while the points of the curve live in , the algebra of multiplying a point by scalars is governed by arithmetic in .
This distinction becomes crucial when reasoning about subgroup structure, constrained scalar ranges, and attack surfaces in cryptographic protocols.
Elliptic curves are not only used in traditional public-key cryptography, but also play a crucial role in zero-knowledge proof systems, particularly in pairing-based SNARKs like Groth16 and PLONK.
Proof systems such as Groth16 and PLONK leverage bilinear pairings between elliptic curve groups to achieve:
A pairing is a special function of the form:
where , , and are groups associated with an elliptic curve (or pair of curves). The function satisfies:
In the Groth16 zk-SNARK protocol, the prover is given:
Using this data, the prover computes a proof consisting of three group elements:
These group elements encode a commitment to the full assignment and prove that it satisfies the circuit's constraints without revealing the private inputs.
The verifier is given:
Let the public input linear combination be:
The verifier accepts the proof if the following pairing equation holds:
Here, is a bilinear pairing function. This equation ensures the consistency of the proof with the QAP (Quadratic Arithmetic Program) representation of the circuit and the correctness of the witness with respect to the public inputs.
All the signal involved in the circuit — inputs, outputs, and intermediate signal — are scalars in the finite field , the scalar field of the elliptic curve.
When you write:
signal input a;
signal input b;
signal output c;
c <== a * b;
you're defining a constraint over three scalars in , and these scalars become part of the proof's internal structure. The QAP ensures these values satisfy the circuit's logic, and the pairing check ensures the prover knows such values without revealing them.
One of the most widely used elliptic curves in zero-knowledge proof systems is BN254, also known as alt_bn128 in Ethereum. It plays a central role in pairing-based SNARKs like Groth16 and PLONK, and is natively supported in the Ethereum Virtual Machine through precompiles for fast verification.
BN254 is a Barreto–Naehrig (BN) curve defined over a 254-bit prime field:
The curve equation is written in short Weierstrass form:
BN254 supports efficient bilinear pairings and has been widely adopted in zk-SNARK implementations. However, this curve is not without caveats, especially in the context of constrained environments like smart contracts.
A concrete example of a security issue that stems from mishandling elliptic curve field sizes occurred in a16z’s ZkDrops, a SNARK-based airdrop system. This vulnerability is documented in the 0xPARC zk-bug-tracker.
ZkDrops requires users to submit a nullifier when claiming an airdrop. This nullifier is supposed to be a unique, deterministic value for each claim and is stored on-chain as a 256-bit integer. The SNARK circuit uses a scalar field of 254 bits (matching the BN254 curve), so any value larger than this is automatically reduced modulo during proof generation.
However, the smart contract did not verify that the nullifier was within the scalar field range. This allowed users to submit two different nullifiers:
which both evaluate to the same value modulo within the SNARK circuit, but appear distinct to the on-chain verifier, which treats them as separate 256-bit integers.
A malicious user could:
This effectively allowed the same airdrop claim to be accepted twice.
function collectAirdrop(bytes calldata proof, bytes32 nullifierHash) public {
require(!nullifierSpent[nullifierHash], "Airdrop already redeemed");
uint[] memory pubSignals = new uint[](3);
pubSignals[0] = uint256(root);
pubSignals[1] = uint256(nullifierHash);
pubSignals[2] = uint256(uint160(msg.sender));
require(verifier.verifyProof(proof, pubSignals), "Proof verification failed");
nullifierSpent[nullifierHash] = true;
airdropToken.transfer(msg.sender, amountPerRedemption);
}
The fix was to add a range check in the smart contract to ensure that the nullifier lies within the scalar field:
require(uint256(nullifierHash) < SNARK_FIELD ,"Nullifier is not within the field");
This guarantees that the on-chain nullifier matches the one used inside the SNARK circuit, preventing duplication via modular reduction.
In zk-SNARK circuits based on BN254, all in-circuit arithmetic takes place in the scalar field . To implement elliptic curve operations such as Pedersen hashes or EdDSA signatures within these circuits, we need a curve defined over . This is the role of Baby-Jubjub, a twisted Edwards curve designed for in-circuit use.
Baby-Jubjub is defined over the BN254 scalar field:
This allows Baby-Jubjub points to be represented and manipulated using arithmetic inside a SNARK circuit. The curve has the following structure:
This means Baby-Jubjub has a prime-order subgroup of size , but the overall curve has small subgroups due to the cofactor.
In a recent audit of AvaCloud, we found a vulnerability in the handling of scalar values used in Baby-Jubjub scalar multiplication. Specifically:
The base point of Baby-Jubjub has order (BN254 scalar field size), but scalar inputs are taken from the full scalar field . Without a check that scalars lie in the correct range (i.e., less than ), two distinct scalars can produce the same curve point when multiplied by the base point.
This is because elliptic curve scalar multiplication is defined modulo the group order . As a result:
This means a malicious prover can submit different scalar values — such as and — that yield the same Baby-Jubjub point. These are aliasing values: different scalars that map to the same point.
These aliasing values enabled the following attack:
This effectively allowed users to withdraw more funds than they had deposited, by taking advantage of the lack of a scalar range check.
For more details on the Baby-Jubjub scalar aliasing vulnerability, see the full audit report here.
Subgroup attacks arise when a cryptographic system fails to properly constrain the values it operates on — whether those values are scalars, group elements, or curve points. As we've seen, even simple algebraic oversights like a missing range check can have serious consequences.
These bugs stem from the same underlying principle: if a value lives in a larger structure than the one intended, and no check is in place to enforce the correct domain, unexpected behavior will follow.
In zero-knowledge cryptography, these issues are especially tricky because of the complexity of proving and verifying computations across different mathematical domains (groups, fields, and curves). Careful validation and awareness of group structure — particularly order, cofactors, and subgroups — is crucial to ensuring soundness.